Enable Hybrid Modern Authentication for on-premises Skype for Business and Exchange servers – Part 2 SFB
In this post we will configure Hybrid Modern Authentication (HMA) on our on-premises Skype for Business Server.
This post is split into two parts, in part 1 we configure HMA for Exchange and in part 2 for Skype for Business.
About modern authentication and HMA you will find in my following post all necessary information.
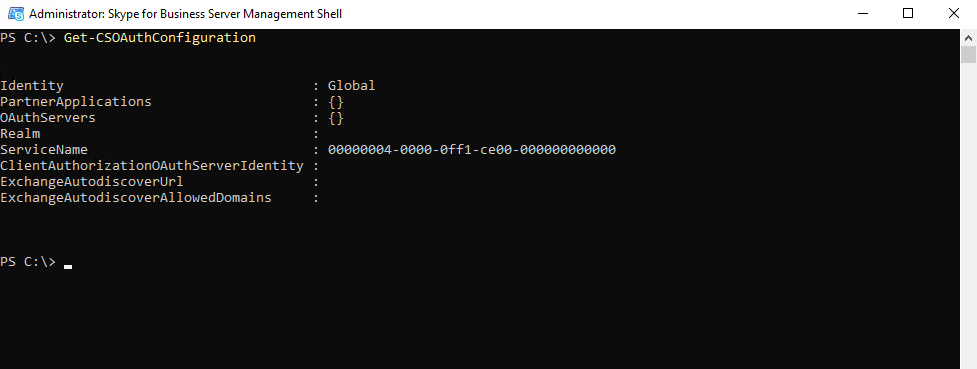
First we check the status on our on-premises Skype for Business Server by running the following PowerShell command:
Get-CSOAuthConfiguration
If the command returns an empty OAuthServers property, or if the value of the ClientADALAuthOverride property is not Allowed, then modern authentication is disabled.
For more information about the Get-CsOAuthConfiguration cmdlet, see Get-CsOAuthConfiguration.
Also on my on-premises Skype for Business server in my lab environment, modern authentication is disabled.
After that check if your on-premises environment meets the prerequisites for modern authentication.
Skype for Business topologies supported with Modern Authentication
https://docs.microsoft.com/en-us/skypeforbusiness/plan-your-deployment/modern-authentication/topologies-supported
Now we can configure our on-premises Skype for Business Server to use Hybrid Modern Authentication.
Modern Authentication, is a method of identity management that offers more secure user authentication and authorization, is available for Skype for Business server on-premises and Exchange server on-premises, and split-domain Skype for Business hybrids.
I will use the following post from Microsoft to configure it.
How to configure Skype for Business on-premises to use Hybrid Modern Authentication
https://docs.microsoft.com/en-us/microsoft-365/enterprise/configure-skype-for-business-for-hybrid-modern-authentication
Turn on Modern Authentication for Skype for Business Online
Before you enable modern authentification for your on-premises environment, please check that you enabled it first for Skype for Business Online.
Follow the instructions here: Skype for Business Online: Enable your tenant for modern authentication.
First we will create a file to hold the info you’ll need for configuring HMA in the steps ahead.
- SIP/SMTP domain
Ex. contoso.com (is federated with Office 365) - Tenant ID
The GUID that represents your Office 365 tenant (at the login of contoso.onmicrosoft.com). - SFB Web Service URLs
you’ll need internal and external web service URLs for all SfB pools deployed. To obtain these, run the following from Skype for Business Management Shell:
Get-CsService -WebServer | Select-Object PoolFqdn, InternalFqdn, ExternalFqdn | FL
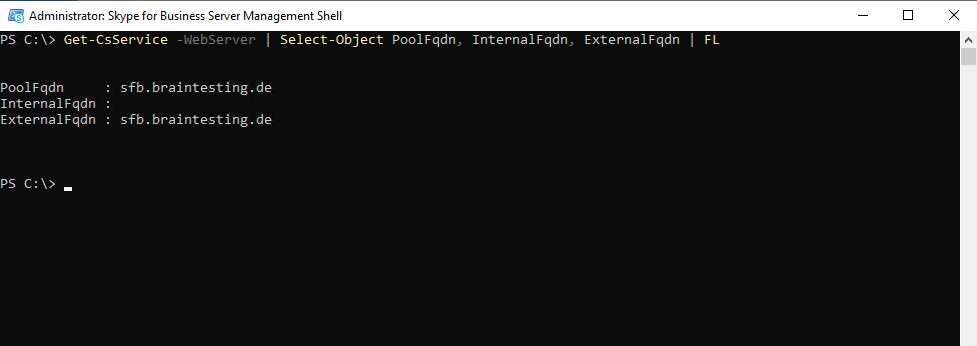
If you’re using a Standard Edition server as in my case, the internal URL will be blank. In this case, use the pool fqdn for the internal URL.
Now we need to add our on-premises web services URLs as SPNs in Azure AD.
Now you’ll need to run commands to add the URLs (collected earlier) as Service Principals in SFBO.
Note Service principal names (SPNs) identify web services and associate them with a security principal (such as an account name or group) so that the service can act on the behalf of an authorized user. Clients authenticating to a server make use of information that’s contained in SPNs.
Now we need to connect to the Azure AD using the Connect-MsolService command as follows.
Connect-MsolService
# For your SFB-related URLs, type the following command:
Get-MsolServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000 | Select -ExpandProperty ServicePrincipalNames
The Application ID 00000004-0000-0ff1-ce00-000000000000 belongs to Skype for Business Online which you can see in Azure Enterprise applications.
Take note of (and screenshot for later comparison) the output of this command, which will include an SE and WS URL, but mostly consist of SPNs that begin with 00000004-0000-0ff1-ce00-000000000000/.

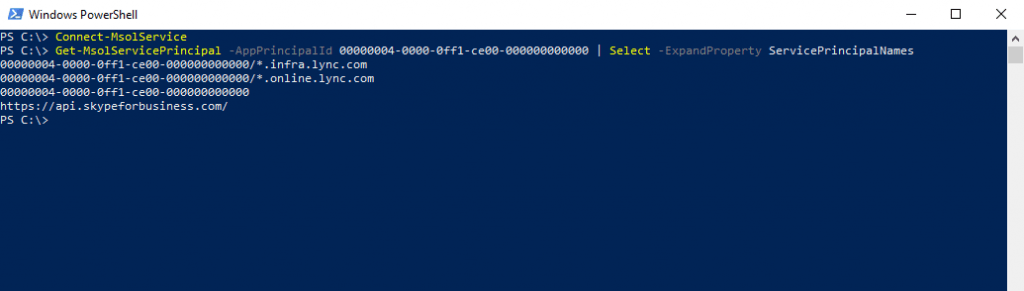
If the internal or external SFB URLs from on-premises are missing (for example, https://lyncwebint01.contoso.com and https://lyncwebext01.contoso.com) we will need to add those specific records to this list.
Be sure to replace the example URLs below with your actual URLs in the Add commands!
$x= Get-MsolServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000
$x.ServicePrincipalnames.Add("https://lyncwebint01.contoso.com/")
$x.ServicePrincipalnames.Add("https://lyncwebext01.contoso.com/")
Set-MSOLServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000 -ServicePrincipalNames $x.ServicePrincipalNamesSo in my case I have to add https://sfb.braintesting.de/ as follows
$x= Get-MsolServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000
$x.ServicePrincipalnames.Add("https://sfb.braintesting.de/")
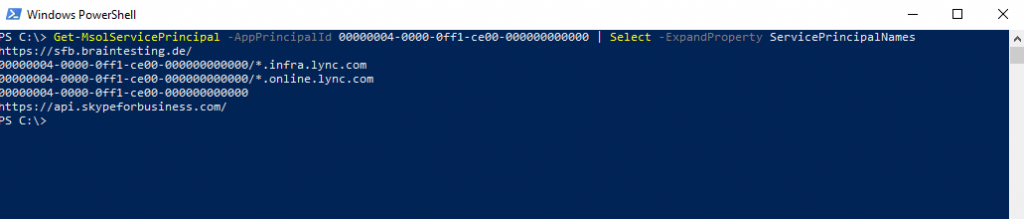
Set-MSOLServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000 -ServicePrincipalNames $x.ServicePrincipalNamesAfter that another check with
Get-MsolServicePrincipal -AppPrincipalId 00000004-0000-0ff1-ce00-000000000000 | Select -ExpandProperty ServicePrincipalNames
Verify your new records were added by running the Get-MsolServicePrincipal command from step 2 again, and looking through the output. Compare the list or screenshot from before to the new list of SPNs.
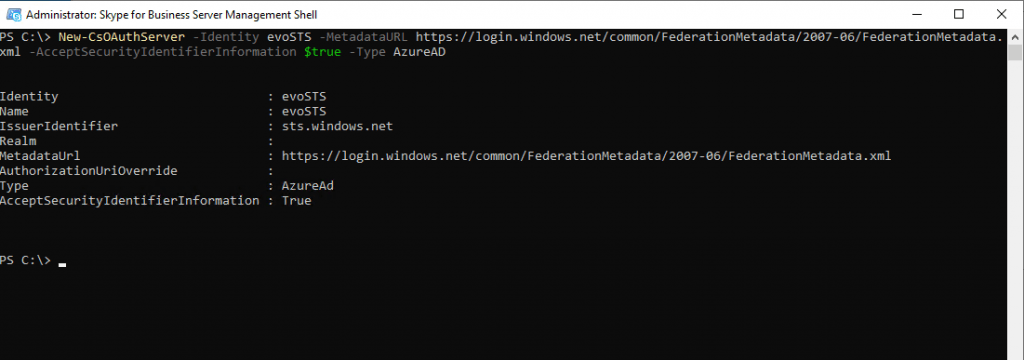
Run the following command in your on-premises Skype for Business Management Shell to create the EvoSTS Auth Server Object.
New-CsOAuthServer -Identity evoSTS -MetadataURL https://login.windows.net/common/FederationMetadata/2007-06/FederationMetadata.xml -AcceptSecurityIdentifierInformation $true -Type AzureAD
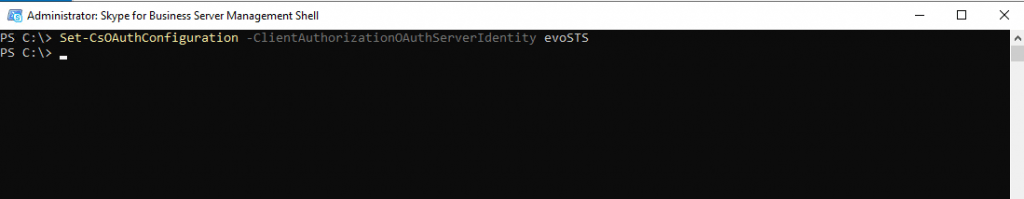
Finally we need to enable the Hybrid Modern Authentification for the on-premise Skype for Business server as follow.
Set-CsOAuthConfiguration -ClientAuthorizationOAuthServerIdentity evoSTS
This is the step that actually turns on MA. All the previous steps can be run ahead of time without changing the client authentication flow. When you’re ready to change the authentication flow, run this command in the Skype for Business Management Shell.
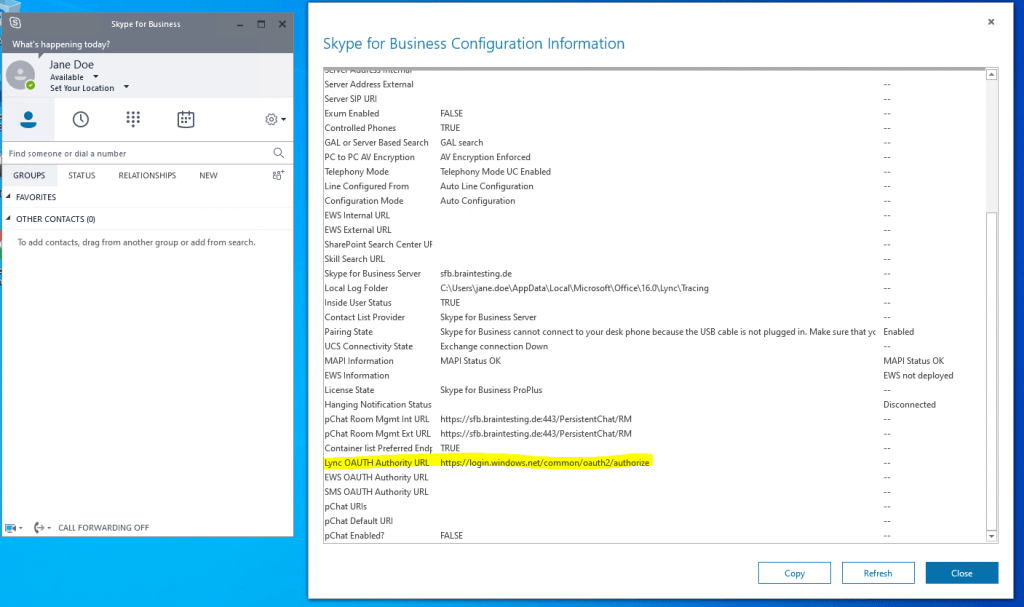
Finally we can verify if the clients will use for the next login HMA.
Once you enable HMA, a client’s next login will use the new auth flow. Note that just turning on HMA won’t trigger a reauthentication for any client. The clients reauthenticate based on the lifetime of the auth tokens and/or certs they have.
To test that HMA is working after you’ve enabled it, sign out of a test SFB Windows client and be sure to click ‘delete my credentials’. Sign in again. The client should now use the Modern Auth flow and your login will now include an Office 365 prompt for a ‘Work or school’ account, seen right before the client contacts the server and logs you in.
You should also check the ‘Configuration Information’ for Skype for Business Clients for an ‘OAuth Authority’. To do this on your client computer, hold down the CTRL key at the same time you right-click the Skype for Business Icon in the Windows Notification tray. Click Configuration Information in the menu that appears. In the ‘Skype for Business Configuration Information’ window that will appear on the desktop, look for the following:
You can also force the user to re-authenticate against the new AuthServer, by setting his actual using Token to expired with the following command in the MSOnline PowerShell Module.
Connect-MsolService Set-MsolUser -UserPrincipalName jdoe@braintesting.de -StsRefreshTokensValidFrom $([System.DateTime]::UtcNow)
Disable Modern Authentication
In case you will run into trouble with modern authentification, like the Azure AD and Office 365 service fails or your local companies internet connection fails, you can quickly disable modern authentification as follows.
Keep in mind, that with HMA, also the on-premise users depends on Azure AD to authenticate against Exchange.
# for Exchange on-premise Set-AuthServer -Identity evoSTS -IsDefaultAuthorizationEndpoint $false # for Skype for Business on-premise Set-CsOAuthConfiguration -ClientAuthorizationOAuthServerIdentity ""
Links
How to configure Skype for Business on-premises to use Hybrid Modern Authentication
https://docs.microsoft.com/en-us/microsoft-365/enterprise/configure-skype-for-business-for-hybrid-modern-authentication
Skype for Business topologies supported with Modern Authentication
https://docs.microsoft.com/en-us/skypeforbusiness/plan-your-deployment/modern-authentication/topologies-supported
Skype for Business Online: Enable your tenant for modern authentication
https://social.technet.microsoft.com/wiki/contents/articles/34339.skype-for-business-online-enable-your-tenant-for-modern-authentication.aspx
Hybrid modern authentication overview and prerequisites for using it with on-premises Skype for Business and Exchange servers
https://docs.microsoft.com/en-us/microsoft-365/enterprise/hybrid-modern-auth-overview?view=o365-worldwide
Tags In
Latest posts
Modern Azure Deployments with Terraform & GitHub – Part 3 – Automating Terraform CI/CD Workflows with GitHub Actions
Follow me on LinkedIn


