How to set up a Custom Certificate on the Dell PowerVault ME5024 Storage Array
By default, the Dell PowerVault ME5024 storage comes with a self-signed certificate assigned to its both Management Controller (MC).
Management Controller (MC) and Storage Controller (SC) are separate subsystems on ME series arrays.
The Management Controller (MC) handles management and monitoring of the storage system and the Storage Controller (SC) handles data processing, RAID operations, and I/O traffic.
The separation of MC and SC in ME series arrays improves reliability, management tasks don’t interfere with data processing, and failures in one subsystem don’t necessarily crash the other. This design is common in modern storage systems for better fault isolation and performance.
In this post we will see how we can create and place a custom certificate for the ME series arrays and its Management Controller (MC).
Create the Certificate Signing Request (CSR) on each Controller
The Dell PowerVault ME5024 storage comes with two Management Controller (MC), controller A and B.
To create a new custom certificate to finally replace its default self-signed certificate, we first need to create a certificate signing request (CSR) on each of the controllers which we can use to get a certificate by a CA which is signing our CSR.
In public key infrastructure (PKI) systems, a certificate signing request (CSR or certification request) is a message sent from an applicant to a certificate authority of the public key infrastructure (PKI) in order to apply for a digital identity certificate.
The CSR usually contains the public key for which the certificate should be issued, identifying information (such as a domain name) and a proof of authenticity including integrity protection (e.g., a digital signature).
Source: https://en.wikipedia.org/wiki/Certificate_signing_request
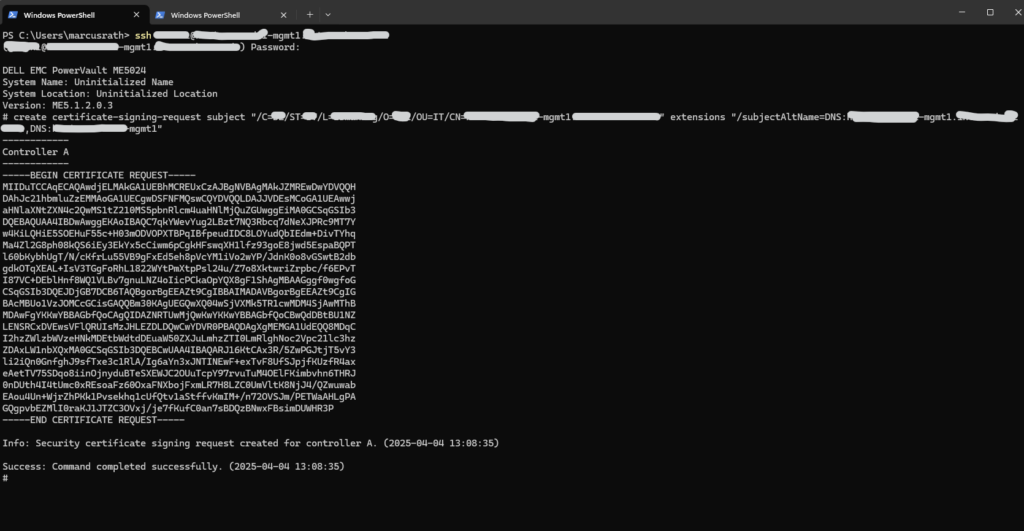
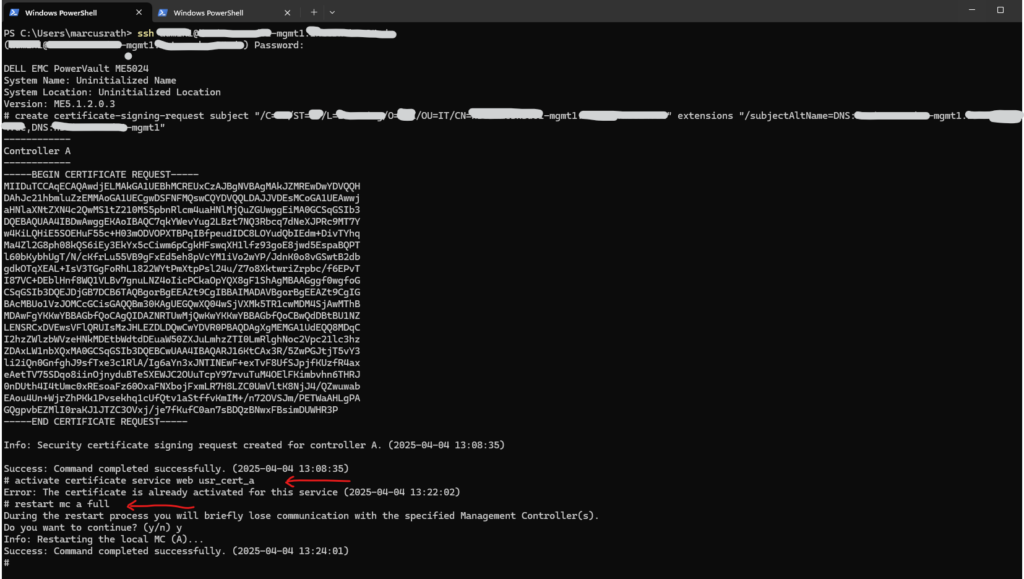
To create the certificate signing request (CSR) we need to connect to by using its SSH console. First I will connect to controller A. Then we need to run the create certificate-signing-request command as shown below. This command will create the CSR and private key, the CSR we then need to take to a CA to get a certificate.
Controller A
# create certificate-signing-request subject "/C=US/ST=CA/L=LAX/O=Matrixpost/OU=IT/CN=me5024-mgmt1.matrixpost-lab.net" extensions "/subjectAltName=DNS:me5024-mgmt1.matrixpost-lab.net,DNS:me5024-mgmt1"
Request the Certificate by a CA
We can now use the CSR to request a custom certificate by either a public or private CA. I will use here my own PKI (AD CS) to sign the CSR and to finally get the certificate.
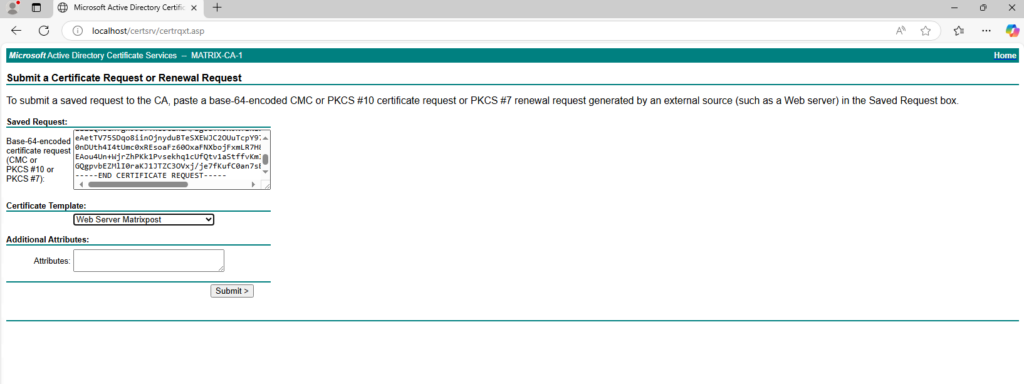
About how to set up a PKI by using the Active Directory Certificate Services (AD CS), you can read my following post.
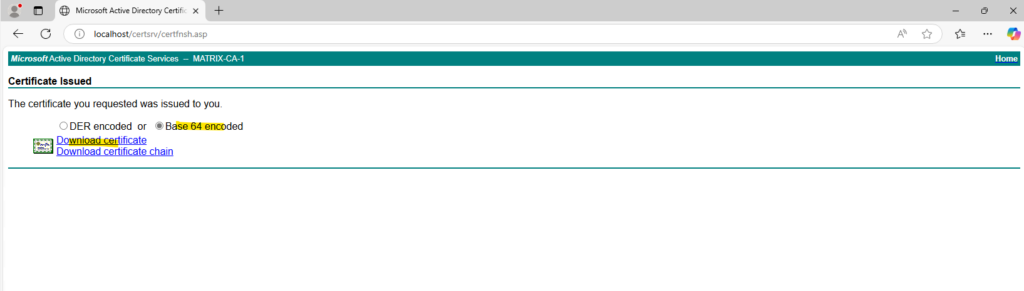
We can now download the certificate, we need to download it in base64-encoded.
Upload the Certificate to the Management Controller (MC)
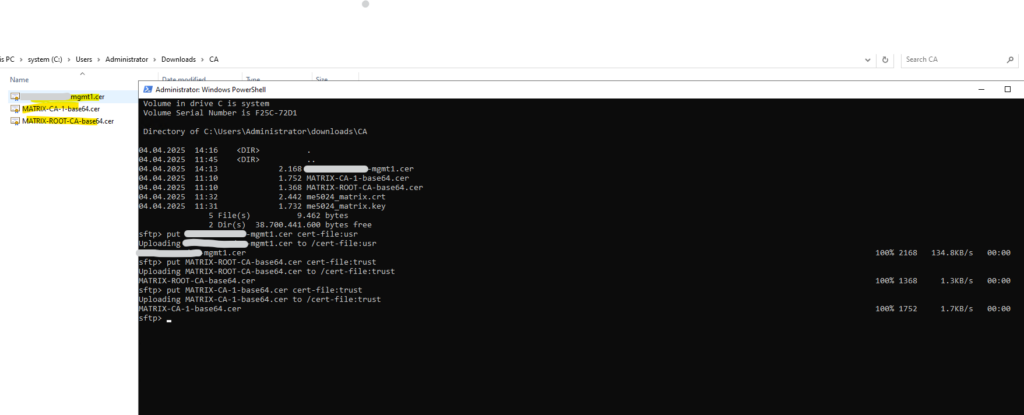
Next we need to upload this certificate to the Management Controller (MC) by using ftp or sftp, below I will use SFTP.
So I will connect to the Management Controller (MC) A on which we created previously the CSR, and therefore the corresponding private key is already stored on, by using the sftp command and utility on Windows.
By default the Dell PowerVault ME5024 will use TCP port 1022 for SFTP.
First I will upload the certificate and next the root certificate and intermediate of my CA. The certificate we need to upload by using the usr role and the root and intermediate certificates by using the trust role. (first the certificate file name and then the flag cert-file:<role>).
PS> sftp -P 1022 sftpuser@me5024-mgmt1.matrixpost-lab.net sftp> put me5024-mgmt1.cer cert-file:usr sftp> put MATRIX-ROOT-CA-base64.cer cert-file:trust sftp> put MATRIX-CA-1-base64.cer cert-file:trust
Activate the Certificate on the Management Controller (MC) and its Web Service.
We can now activate the certificate for the web service on the Management Controller (MC) and finally restart the controller.
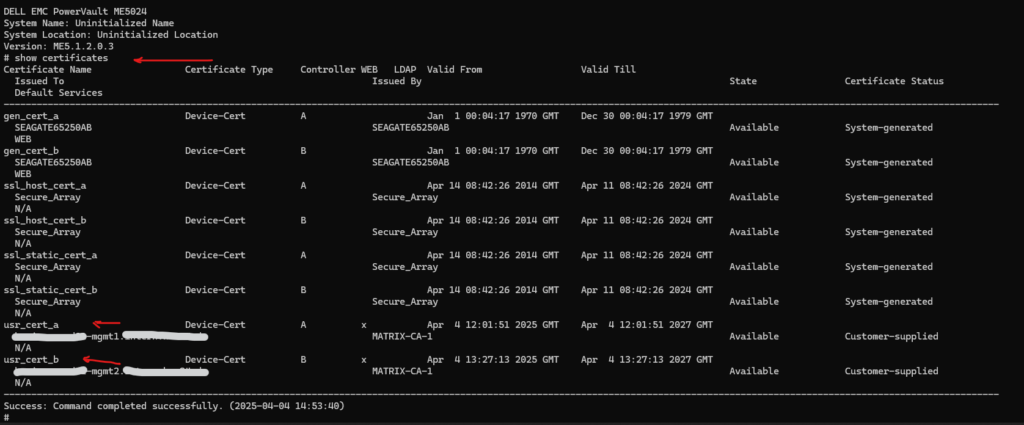
On controller A the uploaded custom certificate name is always usr_cert_a and on controller B it is usr_cert_b.
Sometimes even despite uploaded the certs, the usr_cert_a and usr_cert_b are not available when running the show certificates command. Then you will run into Error: Invalid certificate name. So repeat the upload using sftp and check if the certificates are listed before running the commands below.
# activate certificate service web usr_cert_a # restart mc a full
In my case the certificate was already activated, so I actually just needed to restart the controller.
The certificates available on the controller we can display by using the following command.
# show certificates
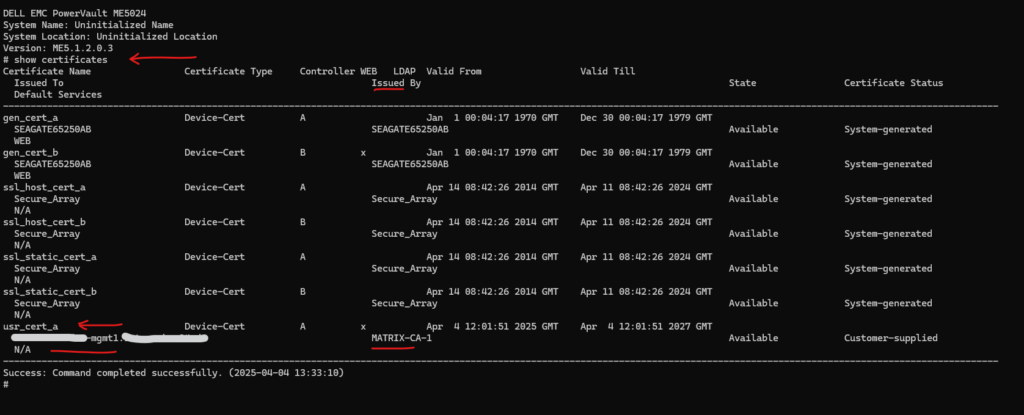
Finally we need to perform the same steps for controller B.
Removing Certificates
To remove these certificates we just need to run the following commands.
# remove certificate usr_cert_a # remove certificate usr_cert_b
Links
PowerVault ME5024
https://www.dell.com/en-us/shop/ipovw/powervault-me5024Dell PowerVault ME5 Series Administrator’s Guide
https://www.dell.com/support/manuals/en-us/powervault-me5024/me5_series_ag/configuring-and-provisioning-a-new-storage-system?guid=guid-8fa9691e-d503-4859-8031-a915c4718217&lang=en-usInstalling a security certificate
https://www.dell.com/support/manuals/en-us/powervault-me5024/me5_series_ag/installing-a-security-certificate?guid=guid-97c36507-d19b-402f-aee3-3d684c78db01&lang=en-usPowerVault Manager ME5024 – Custom Certificates Creation and Installation
https://www.goline.ch/2024/12/03/powervault-manager-me5024-custom-certificates-creation-and-installation/
Tags In
Related Posts
Follow me on LinkedIn


