Nikto Web Server Scanner
In this post I want to show how to install and using the nikto command-line vulnerability scanner.
Introduction
Nikto is an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6700 potentially dangerous files/programs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers. It also checks for server configuration items such as the presence of multiple index files, HTTP server options, and will attempt to identify installed web servers and software. Scan items and plugins are frequently updated and can be automatically updated.
Nikto is not designed as a stealthy tool. It will test a web server in the quickest time possible, and is obvious in log files or to an IPS/IDS. However, there is support for LibWhisker’s anti-IDS methods in case you want to give it a try (or test your IDS system).
Source: https://cirt.net/nikto2
Installation
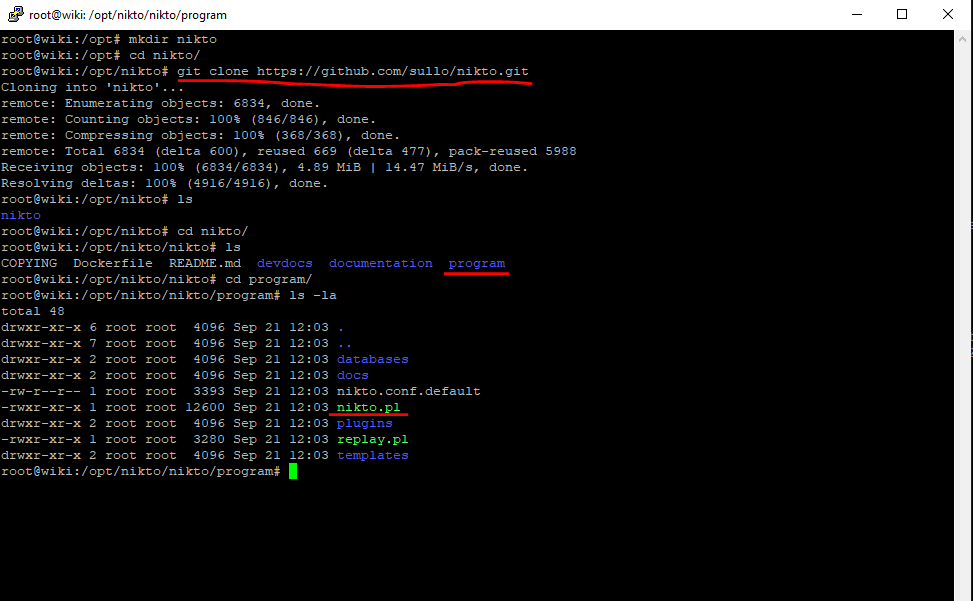
Linux
The installation for Linux and Windows can be done by using the git clone command.
$ git clone https://github.com/sullo/nikto.git
After that you can go to the program directory where you will find the nikto.pl perl script.
In contrast to Windows, Perl is installed on most Linux distributions by default.
You can also use on most distributions the install program as it is available by default in their system repositories.
For Ubuntu you can use:
$ apt update
$ apt install nikto
By installing Nikto this way, you do not have to prefix with the perl command.
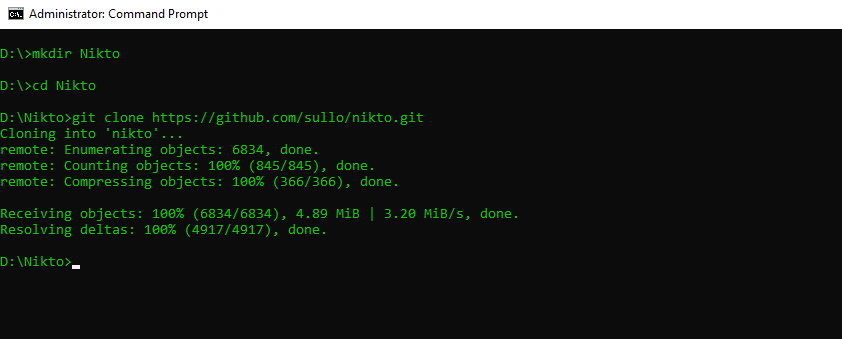
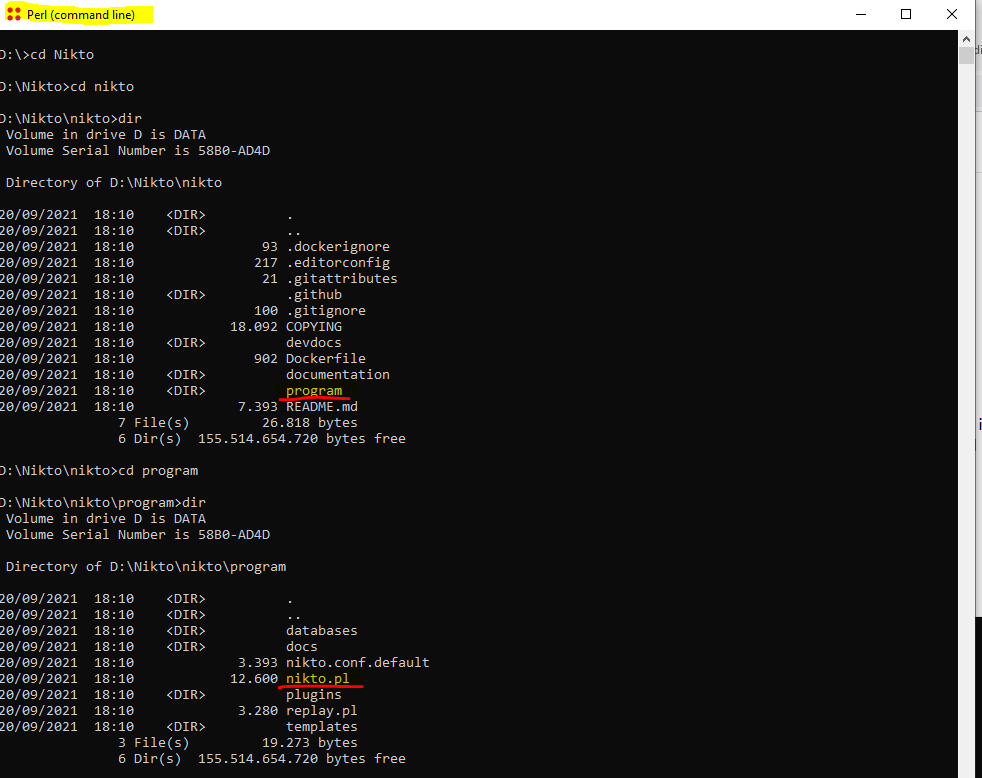
Windows
In order to use Nikto on Windows, you first need to install the latest version of Perl as mentioned above if not already installed.
After that you can download Nikto by using also the following git clone command as with Linux.
Perl for Windows
https://www.perl.org/get.html
Strawberry Perl: A 100% Open Source Perl for Windows that is exactly the same as Perl everywhere else; this includes using modules from CPAN, without the need for binary packages. Help is available from other Windows Perl developers on the #win32 irc channel on irc.perl.org (see website for access through a browser).
https://github.com/sullo/nikto
> git clone https://github.com/sullo/nikto.git
The actual Nikto Perl script nikto.pl, you will find inside the program folder.
Show Help, you can also use the option -help to list all options.
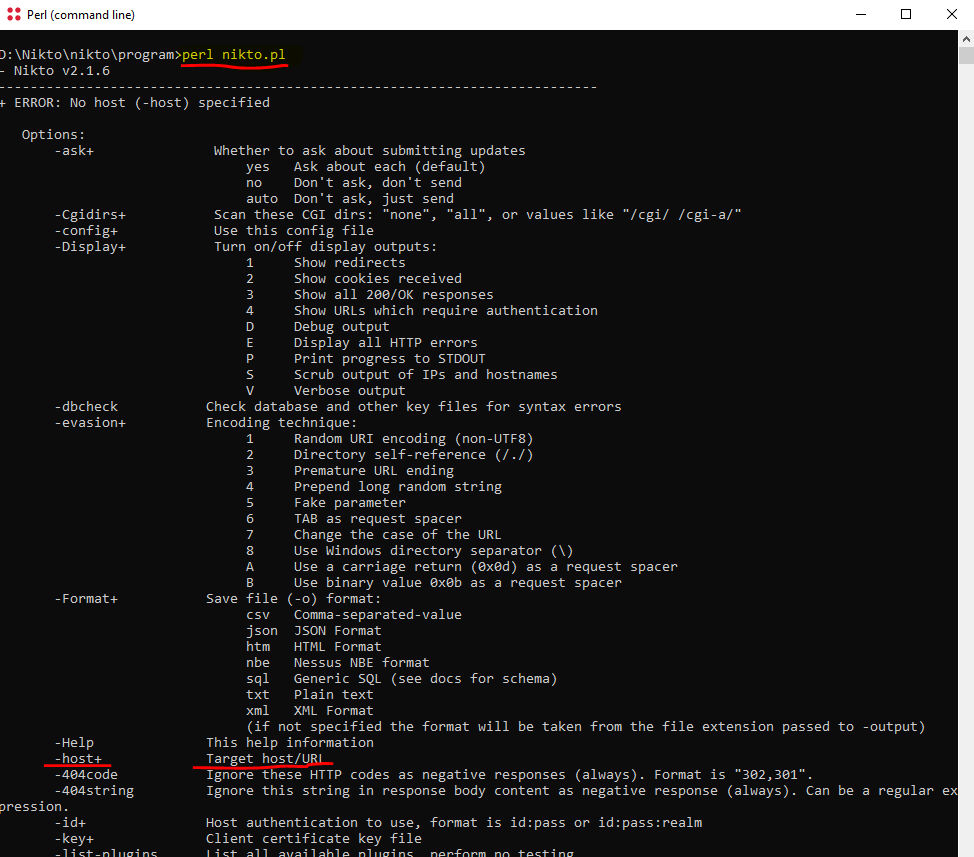
> perl nikto.pl -host https://host.domain.tld/
> perl nikto.pl -url https://host.domain.tld -ssl
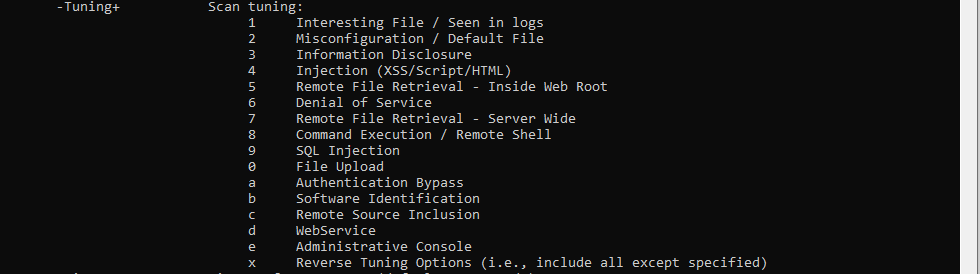
Tuning parameter
> perl nikto.pl -Tuning 123bde -host https://host.domain.tld -ssl
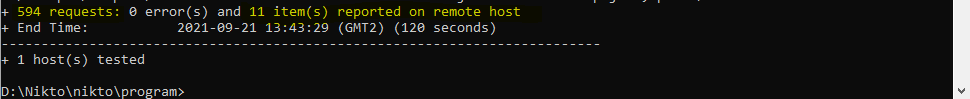
After a scan you will find at the end how many requests were run against the web server and how many vulnerabilities (items on remote host) where found.
To determine what items exactly found on the remote server, you can use the following switch
-o report.html -Format htm
> perl nikto.pl -o report.html -Format htm -host https://host.domain.tld:443/
Finally you will find a report.html file in the directory you executed the command.
Testing Examples
Basic Testing
https://github.com/sullo/nikto/wiki/Basic-Testing
Single Port
$ perl nikto.pl -h https://host.domain.tld:443/
$ perl nikto.pl -h 127.0.0.1:443/
Multiple Port
$ perl nikto.pl -h 192.168.0.1 -p 80,88,443
SecRuleEngine On
perl nikto.pl -h <IP to test> -p 80,443
See the documentation for a full list of features and how to use them.
Troubleshooting
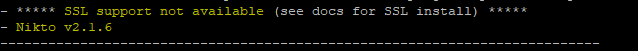
If you want to test an SSL host and will run into the following error, you need to install additional libraries.
$ perl nikto.pl -h <IP to test> -p 443 -ssl
Nikto – SSL Support not available (see docs for SSL install)
You need to install additional libraries
$ apt-get install perl libnet-ssleay-perl openssl libauthen-pam-perl libio-pty-perl
Links
Nikto2
https://cirt.net/nikto2
Install
https://github.com/sullo/nikto
Download latest GitHub Release
https://github.com/sullo/nikto/archive/master.zip
Documentation
https://github.com/sullo/nikto/wiki
Nikto Kali Tools
https://tools.kali.org/information-gathering/nikto
Nikto (vulnerability scanner)
https://en.wikipedia.org/wiki/Nikto_(vulnerability_scanner)
8 SaaS Web Vulnerability Scanner for Continuous Security
https://geekflare.com/saas-web-vulnerability-scanner/
Tags In
Related Posts
Latest posts
Windows Secure Boot Certificates Expire in June and October 2026 – Readiness Checks, Troubleshooting, and VMware vSphere Fixes
Follow me on LinkedIn


