Restrict Access to Azure and Office 365 by Country
To limit the risk of compromising your Office 365 Tenant, you can limit access by blocked or allowed countries. Also you can limit access by IP ranges.
Below I will show you the steps to configure conditional access by country.
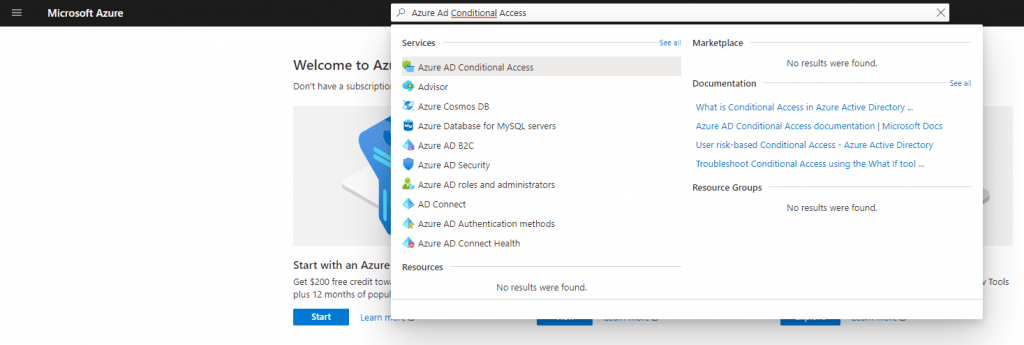
Therefore search for Azure AD Conditional Access.
As you can see, you need an Azure AD Premium licence in order to use Conditional Access Policies.
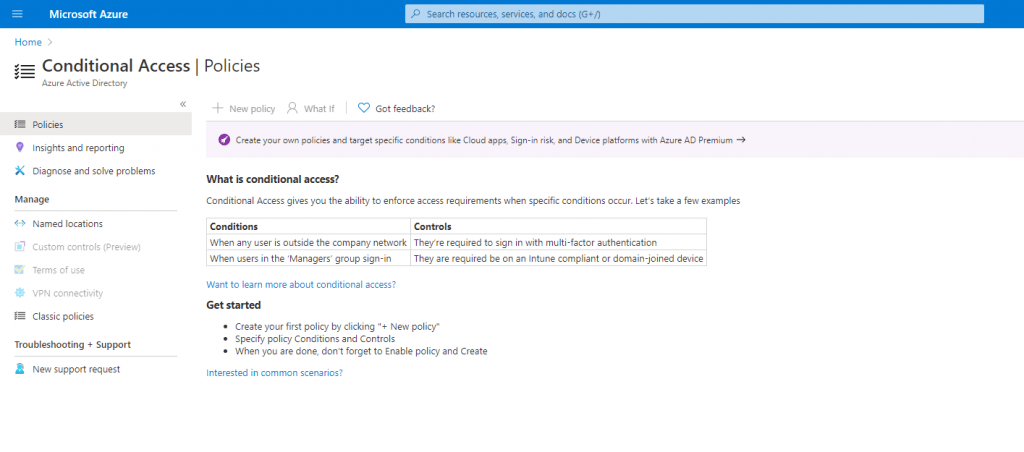
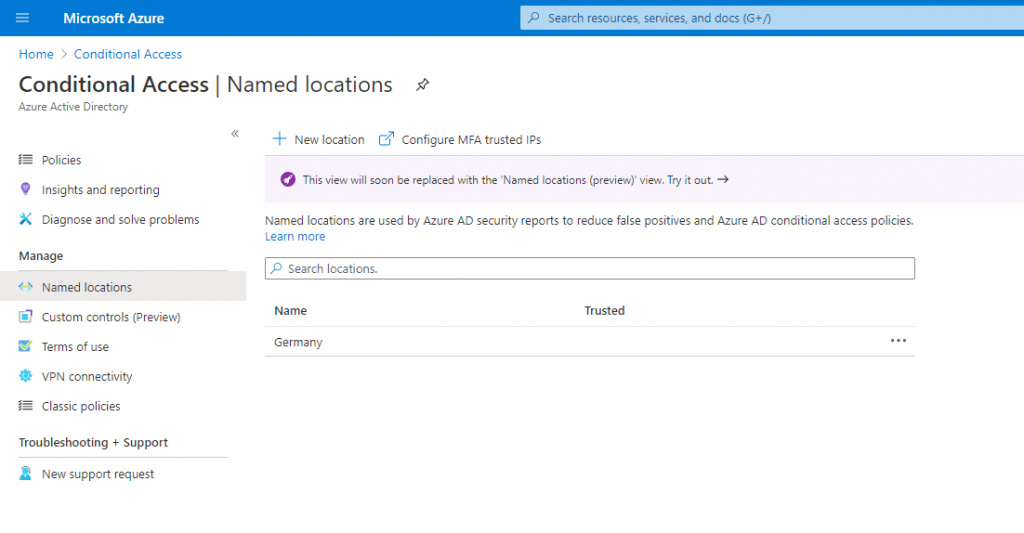
In order to create a new access policy, based on locations, we first need to create a new named location to allow or block them. So click on Named location to create a new one.
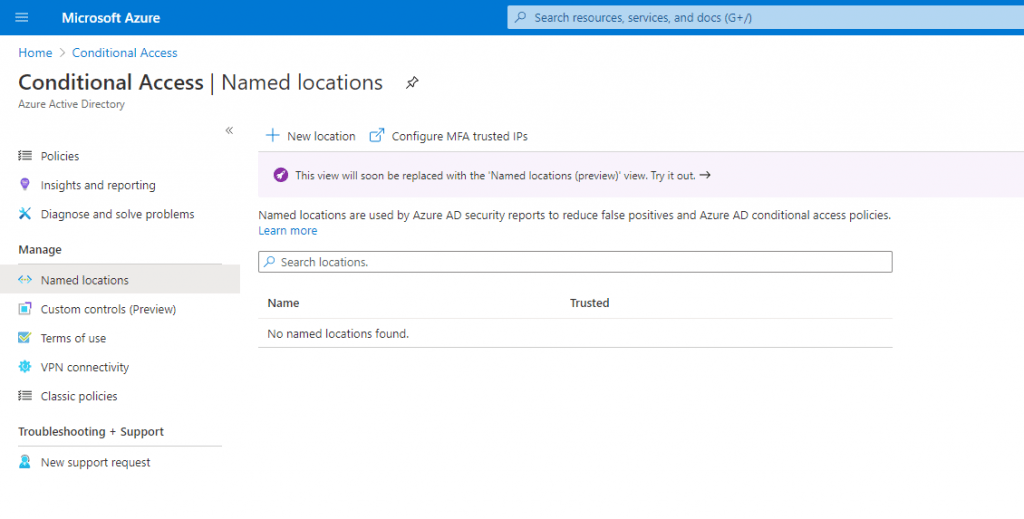
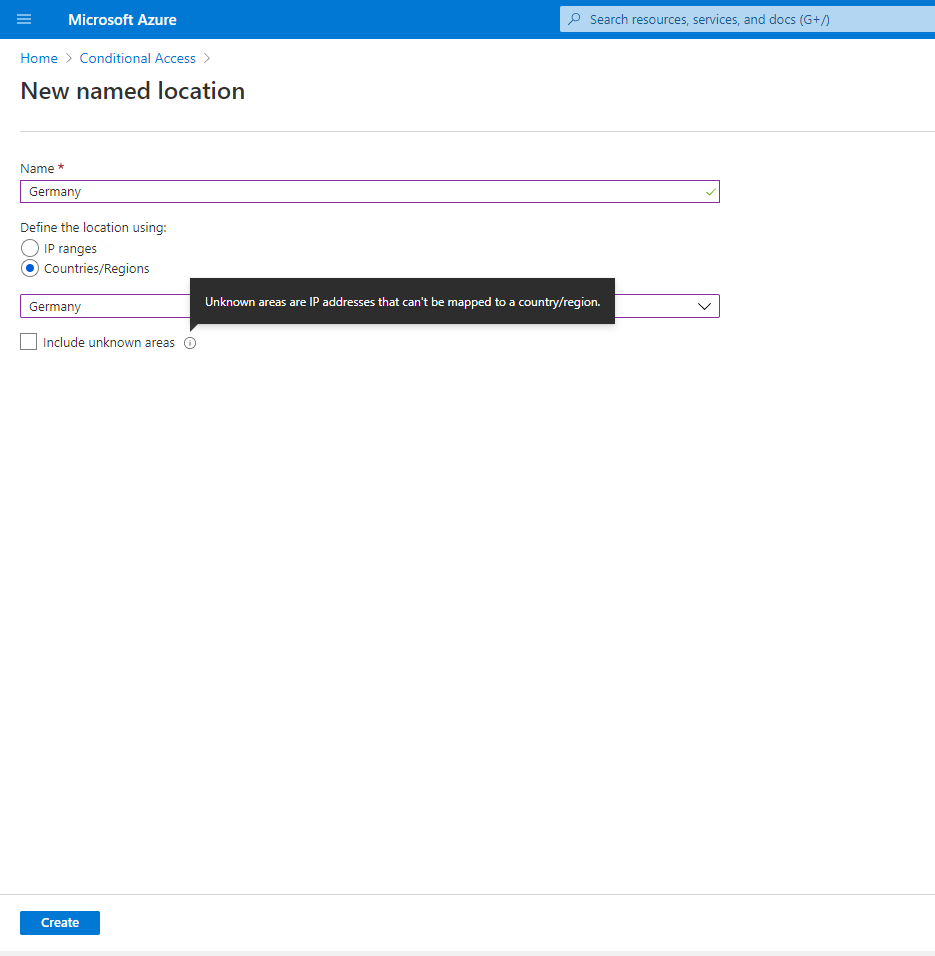
You can choose between IP ranges and Countries in Named locations, so we want to allow access to our tenant only from IPs registered by Germany, I will select Countries/Regions and choose Germany. As you can see, further you have the choice to include unkown areas with IP addresses that can’t be mapped to a country/region.
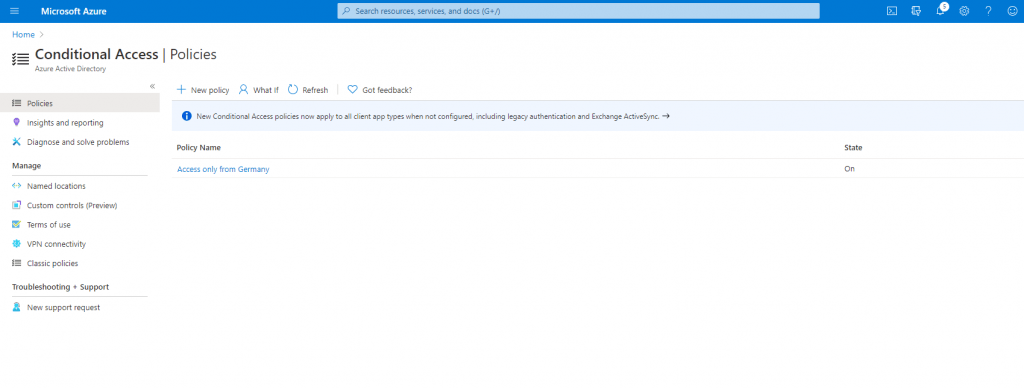
Back on the Conditional Access blade, we can see the new loation.
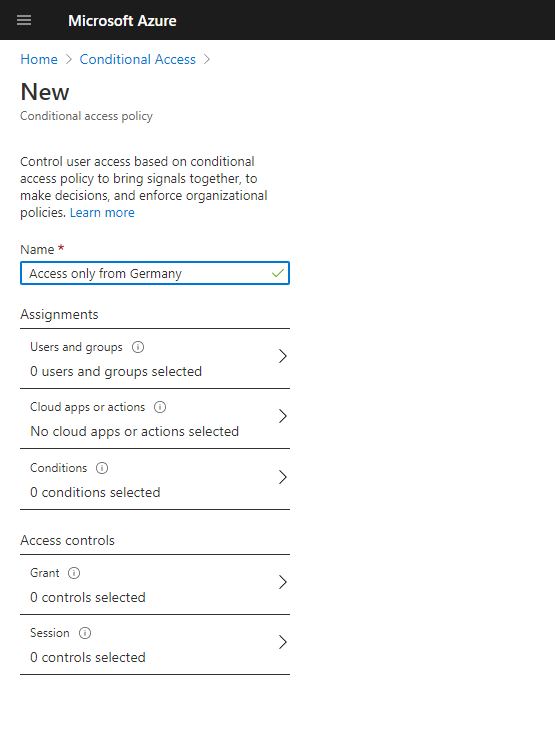
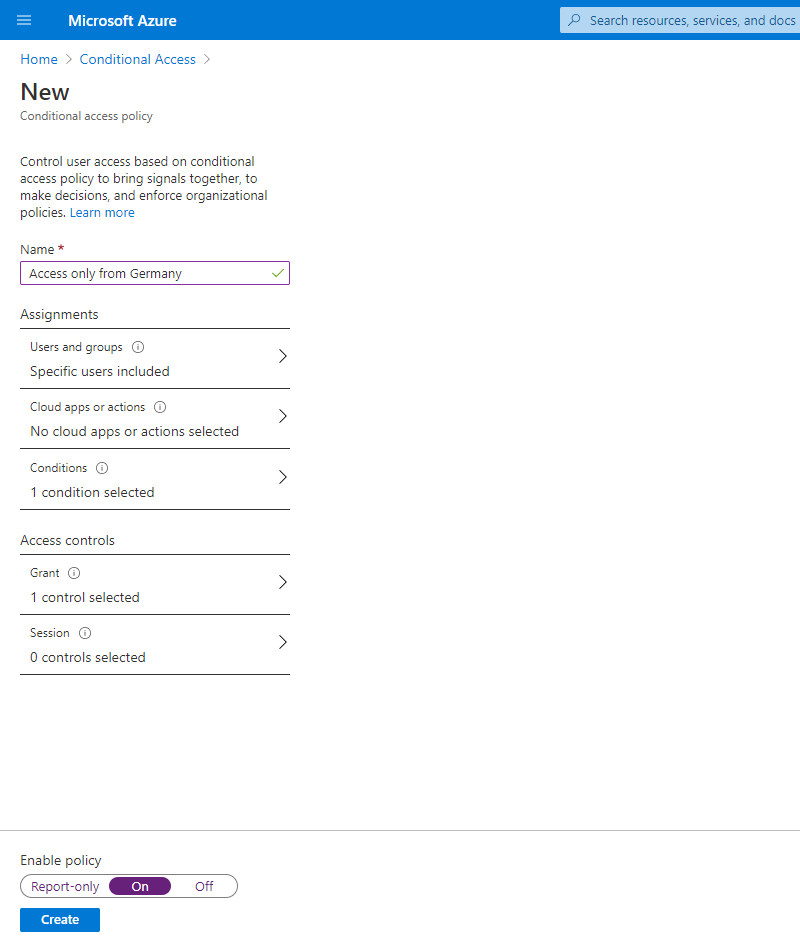
Now we can create the new policy, so select the Policies menu item and click on New policy and enter a useful name for it.
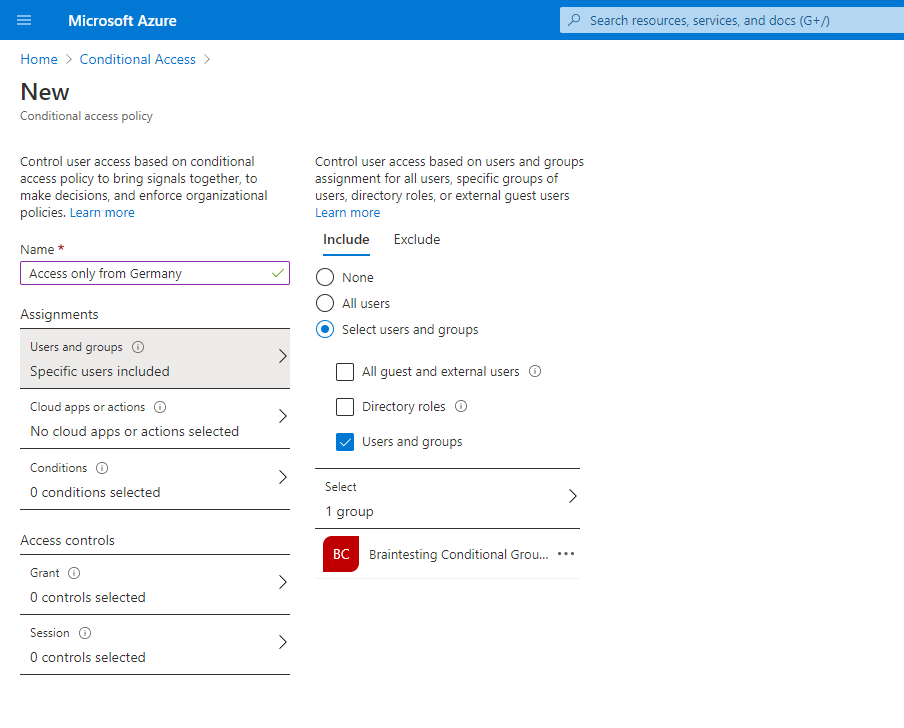
Next you need to assign users and groups the policy will applied to.
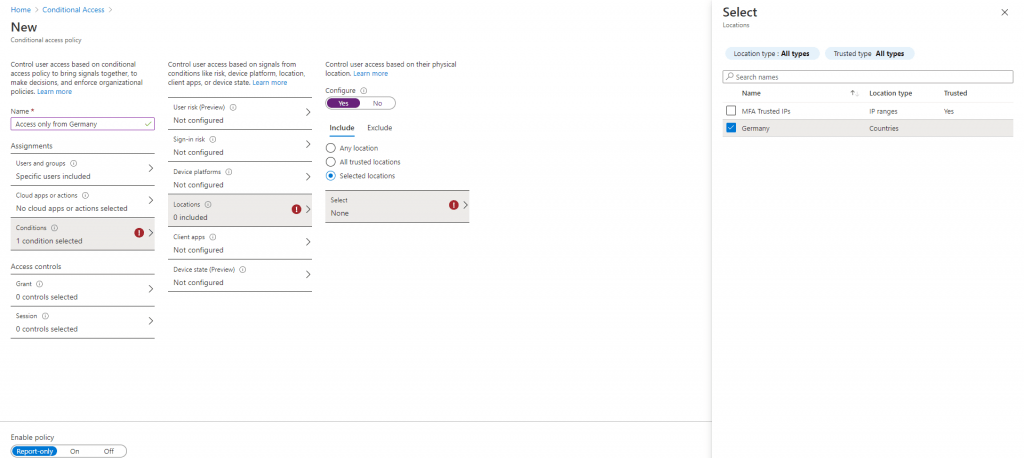
To limit access by Locations, we have to click on Conditions – Locations – Configure yes – Include Selected locations and here we can select our perviously created location Germany.
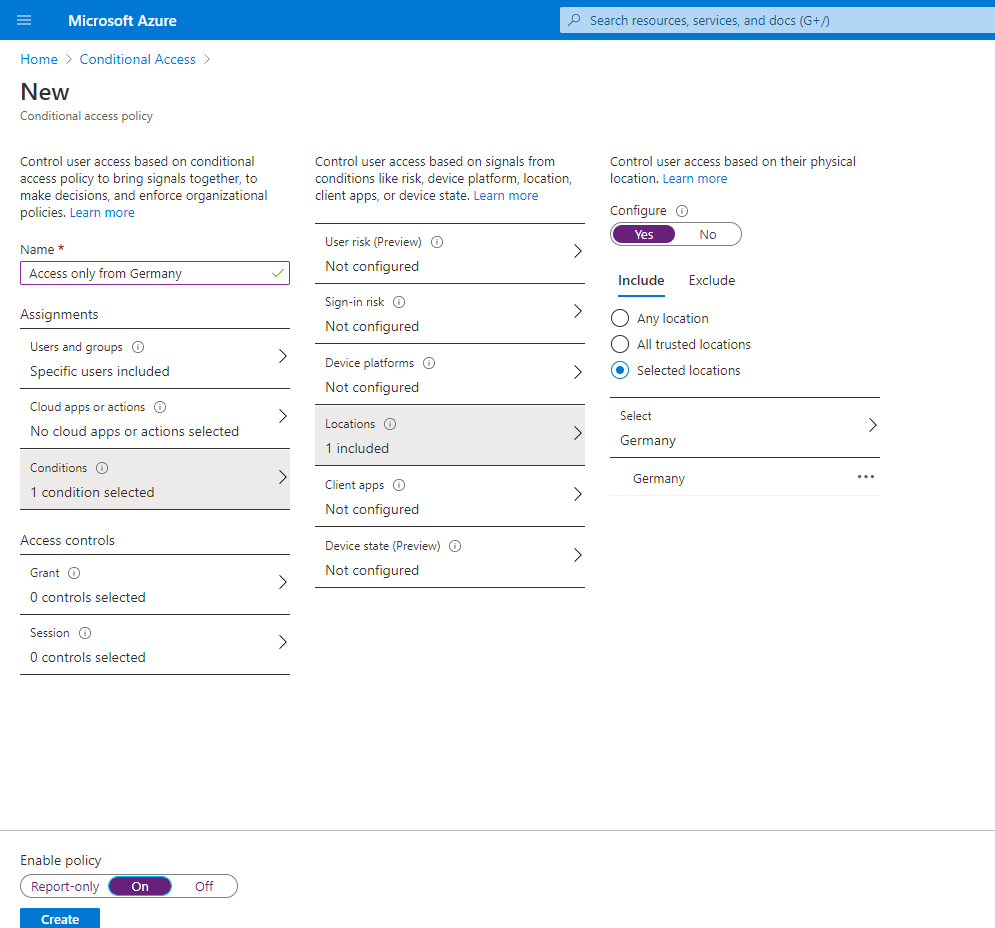
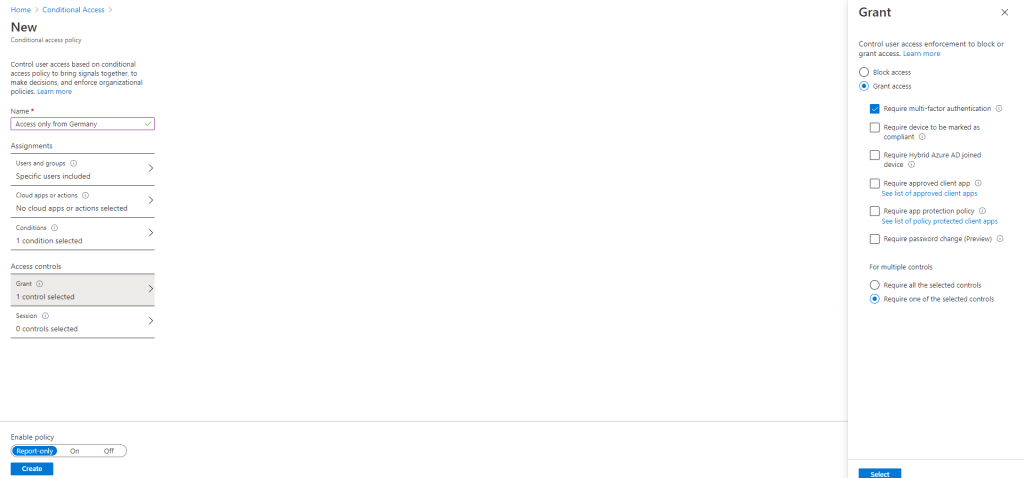
Finally under Access control, you can Block or Grant access for this policy, so as we want to allow all IPs registered by Germany, we select Grant access and Require one of the selected controls.
For Grant access you also have to select one of the controls, I will use here Require multi-factor authentication.
Keep in mind to enable the policy before you click on Create.
Links
What is Conditional Access?
https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/overviewUsing the location condition in a Conditional Access policy
https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/location-condition


