Azure AD B2B (Business-to-business) Federation and Collaboration
In on-permises environments with Active Directory to enable Federation with external companies you have two options, both require specific skills to configure it and additional costs for set up.
- Active Directory Trust Relationships
- Active Directory Federation Services
Now with Azure AD B2B (Business-to-business), federation and collaborattion with external companies and partner organizations became much easier and is an out-of-the-box additional feature of Azure AD.
- Azure AD Editions and Pricing External Identities (Federation and Collaboration)
- Enable and Configure Guest user access
- Bulk invite Azure AD B2B collaboration users
- Azure Active Directory B2B collaboration invitation redemption
- What is Azure AD Identity Governance?
- What is Azure AD entitlement management?
- What are Azure AD access reviews?
- What is Azure AD Privileged Identity Management?
- Links
Azure AD Editions and Pricing External Identities (Federation and Collaboration)
As mentioned below, with all four Azure AD Editions, you can have up to 50.000 active guest users per month without additional costs, provided you have linked your Azure AD tenant to your subscription. More below.
So most customers can use it for free.
Otherwise when your Azure AD tenant is not linked to your subscription, which is by default, rights are granted on a 1:5 ratio. For each user in your tenant, your tenant can invite up to five guest users and leverage the same features as your Azure AD Edition support.
Azure AD Editions Comparison
Azure Active Directory comes in four editions—Free, Office 365 apps (formerly Basic) , Premium P1, and Premium P2.
The Free edition is included with a subscription of a commercial online service, e.g. Azure, Dynamics 365, Intune, and Power Platform. Office 365 subscriptions include the Free edition, but Office 365 E1, E3, E5, F1 and F3 subscriptions also include the features from Office 365 apps.
https://azure.microsoft.com/en-us/pricing/details/active-directory/
Billing model for Azure AD External Identities
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/external-identities-pricing
Azure Active Directory (Azure AD) External Identities pricing is based on monthly active users (MAU), which is the count of unique users with authentication activity within a calendar month. This billing model applies to both Azure AD guest user collaboration (B2B) and Azure AD B2C tenants. MAU billing helps you reduce costs by offering a free tier and flexible, predictable pricing. In this article, learn about MAU billing and linking your Azure AD tenants to a subscription.
If your tenant is an Azure AD tenant already linked to a subscription, you need nothing to do. When you use External Identities feature to collaborate with guest users, you’ll be automatically billed using MAU model.
In your Azure AD tenant, guest user collaboration usage is billed based on the count of unique guest users with authentication activity within a calendar month. This model replaces the 1:5 ratio billing model, which allowed up to five guest users for each Azure AD Premium license in your tenant. When your tenant is linked to a subscription and you use External Identities features to collaborate with guest users, you’ll be automatically billed using the MAU-based billing model.
The pricing tier that applies to your guest users is based on the highest pricing tier assigned to your Azure AD tenant. For example, if the highest pricing tier in your tenant is Azure AD Premium P1, the Premium P1 pricing tier also applies to your guest users. If the highest pricing is Azure AD Free, you’ll be asked to upgrade to a premium pricing tier when you try to use premium features for guest users.
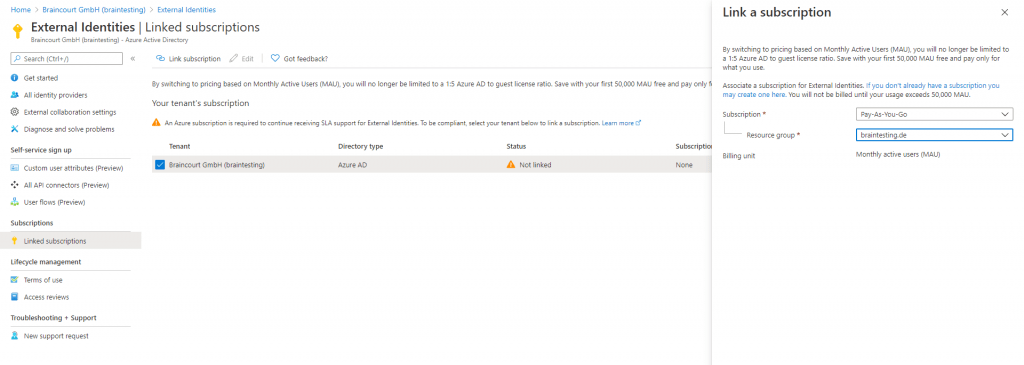
Link your Azure AD tenant to a subscription
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/external-identities-pricing#link-your-azure-ad-tenant-to-a-subscription
Enable and Configure Guest user access
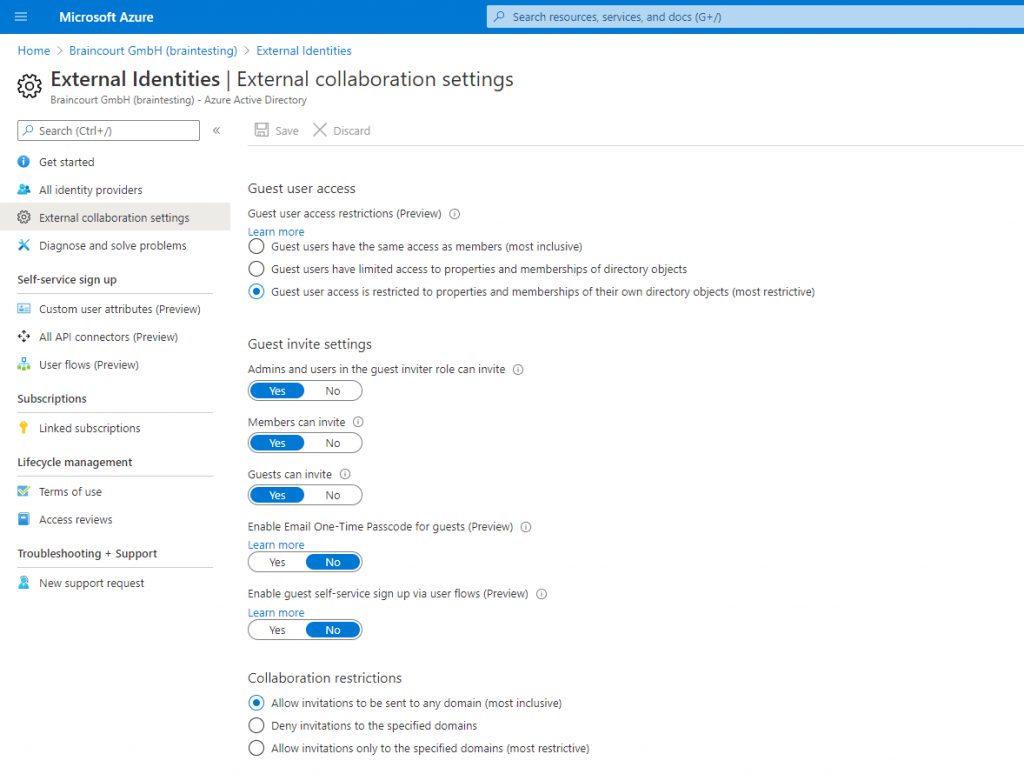
You can configure guest user access in Azure AD – External Identities and there the menu point External collaboration settings.
Bulk invite Azure AD B2B collaboration users
If you use Azure Active Directory (Azure AD) B2B collaboration to work with external partners, you can invite multiple guest users to your organization at the same time. In this tutorial, you learn how to use the Azure portal to send bulk invitations to external users. Specifically, you do the following:
- Use Bulk invite users to prepare a comma-separated value (.csv) file with the user information and invitation preferences
- Upload the .csv file to Azure AD
- Verify the users were added to the directory
Tutorial: Bulk invite Azure AD B2B collaboration users
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/tutorial-bulk-invite
Azure Active Directory B2B collaboration invitation redemption
This article describes the ways guest users can access your resources and the consent process they’ll encounter. If you send an invitation email to the guest, the invitation includes a link the guest can redeem to get access to your app or portal. The invitation email is just one of the ways guests can get access to your resources. As an alternative, you can add guests to your directory and give them a direct link to the portal or app you want to share. Regardless of the method they use, guests are guided through a first-time consent process. This process ensures that your guests agree to privacy terms and accept any terms of use you’ve set up.
When you add a guest user to your directory, the guest user account has a consent status (viewable in PowerShell) that’s initially set to PendingAcceptance. This setting remains until the guest accepts your invitation and agrees to your privacy policy and terms of use. After that, the consent status changes to Accepted, and the consent pages are no longer presented to the guest.
Starting March 31, 2021, Microsoft will no longer support the redemption of invitations by creating unmanaged Azure AD accounts and tenants for B2B collaboration scenarios. In preparation, we encourage customers to opt into email one-time passcode authentication. We welcome your feedback on this public preview feature and are excited to create even more ways to collaborate.
Azure Active Directory B2B collaboration invitation redemption
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/redemption-experience
What is Azure AD Identity Governance?
Azure Active Directory (Azure AD) Identity Governance allows you to balance your organization’s need for security and employee productivity with the right processes and visibility. It provides you with capabilities to ensure that the right people have the right access to the right resources. These and related Azure AD and Enterprise Mobility + Security features allows you to mitigate access risk by protecting, monitoring, and auditing access to critical assets — while ensuring employee and business partner productivity.
Identity Governance give organizations the ability to do the following tasks across employees, business partners and vendors, and across services and applications both on-premises and in clouds:
- Govern the identity lifecycle
- Govern access lifecycle
- Secure privileged access for administration
Specifically, it is intended to help organizations address these four key questions:
- Which users should have access to which resources?
- What are those users doing with that access?
- Are there effective organizational controls for managing access?
- Can auditors verify that the controls are working?
What is Azure AD Identity Governance?
https://docs.microsoft.com/en-us/azure/active-directory/governance/identity-governance-overview
What is Azure AD entitlement management?
Azure Active Directory (Azure AD) entitlement management is an identity governance feature that enables organizations to manage identity and access lifecycle at scale, by automating access request workflows, access assignments, reviews, and expiration.
Employees in organizations need access to various groups, applications, and sites to perform their job. Managing this access is challenging, as requirements change – new applications are added or users need additional access rights. This scenario gets more complicated when you collaborate with outside organizations – you may not know who in the other organization needs access to your organization’s resources, and they won’t know what applications, groups, or sites your organization is using.
Azure AD entitlement management can help you more efficiently manage access to groups, applications, and SharePoint Online sites for internal users, and also for users outside your organization who need access to those resources.
What is Azure AD entitlement management?
https://docs.microsoft.com/en-us/azure/active-directory/governance/entitlement-management-overview
What are Azure AD access reviews?
Azure Active Directory (Azure AD) access reviews enable organizations to efficiently manage group memberships, access to enterprise applications, and role assignments. User’s access can be reviewed on a regular basis to make sure only the right people have continued access.
Why are access reviews important?
Azure AD enables you to collaborate with users from inside your organization and with external users. Users can join groups, invite guests, connect to cloud apps, and work remotely from their work or personal devices. The convenience of using self-service has led to a need for better access management capabilities.
- As new employees join, how do you ensure they have the access they need to be productive?
- As people move teams or leave the company, how do you make sure that their old access is removed?
- Excessive access rights can lead to compromises.
- Excessive access right may also lead audit findings as they indicate a lack of control over access.
- You have to proactively engage with resource owners to ensure they regularly review who has access to their resources.
What are Azure AD access reviews?
https://docs.microsoft.com/en-us/azure/active-directory/governance/access-reviews-overview
What is Azure AD Privileged Identity Management?
Privileged Identity Management (PIM) is a service in Azure Active Directory (Azure AD) that enables you to manage, control, and monitor access to important resources in your organization. These resources include resources in Azure AD, Azure, and other Microsoft Online Services such as Microsoft 365 or Microsoft Intune.
What is Azure AD Privileged Identity Management?
https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-configure
Links
Azure Active Directory B2B best practices
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/b2b-fundamentals
Add B2B collaboration guest users without an invitation link or email
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/add-user-without-invite
Direct federation with AD FS and third-party providers for guest users (preview)
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/direct-federation
Microsoft 365 external sharing and Azure Active Directory (Azure AD) B2B collaboration
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/o365-external-user
Tags In
Related Posts
Latest posts
Deploying NetApp Cloud Volumes ONTAP (CVO) in Azure using NetApp Console (formerly BlueXP) – Part 9 – Azure Key Vault as an External Key Manager: Encryption, Outage Recovery, and Worst-Case HA Testing
Follow me on LinkedIn


